Channels, not Addresses
A simple change will make the internet more secure and decentralized.
The Problem with Addresses
Do you remember the novelty of first getting an email address? Or first hearing the idea that everyone online had a unique IP address? It was such a magical thought— that you could send off a message to anyone, anywhere in the world, just by knowing their address. When early technologists tried to explain how the messages got there, we often used post office metaphors—talking about addresses as mailboxes and ‘routing’ as little postal trucks driving in tubes, handing off these bundles of digital mail at the next station and so on. We were told that it all works magically— something originally designed for surviving nuclear war—but that now we could use it to buy stuff and chat with each other!
We came to identify these addresses with ourselves, saying: “My IP address”, “My email”, and “My Website” (websites are also just IP addresses, but looked up in a giant card catalog called the Domain Name System, or DNS). We claimed various forms of legal ownership over these addresses, vigorously defending and debating them in courts (I remember McDonalds.com). While we were fighting over owning addresses, the business of actually delivering the messages to those addresses got taken over by large companies and became more opaque, confusing, and centralized than the designers of TCP/IP had intended.
The original design for TCP/IP was that everyone more or less knew and trusted who each address belonged to (believe it or not, in the 80s there were printed books with the IP addresses, emails, and true names of literally everyone on the internet), and also that if anyone was a bad actor (sending spam, or trying to knock others offline by sending them too many messages, or lying about what address they were sending a message from) it would be a simple matter of disconnecting the cable(s) going to that person. Notably, this was because the original design assumed that most of the people with addresses were also ‘routers’ - responsible for deciding the best way to forward a message to its destination. The design didn’t contemplate a world where service providers give out anonymous addresses (for a fee) that are then used to send and receive packets with almost no risk of consequences for bad behavior.
This brings us to the broken system we have today: Once I get your address, nothing can stop me from sending you messages. This means that I can send you unwanted emails, and worse yet, sell your email address to others who also want to send you unwanted emails. If I have your IP address, I can send you packets so fast that it knocks your personal computer (or your whole website) offline. Even blockchain, sadly, has replicated this broken design… once I have your address, I can send Bitcoin or Ethereum or porn images or phishing attacks to it, and you can’t stop me. I may have to pay for the transaction, but that only prohibits people with zero money from being bad actors - hardly a step in the right direction. Social Media has replicated all this badness the same way: anonymous people create accounts with some sort of public address or name, and once you have someone’s address you can stalk/torment/troll them until whatever ineffective centralized police system exists is called in to defend you, if there is one there at all. Whether on social media or email or a website, we are all now in a big public free-for-all where there is no cost to sending messages to anyone, and no way to stop receiving them.
And AI is going to make this a lot worse, very quickly. This is part of why I am writing this now. Because AI can create infinite numbers of fake people who can communicate infinitely fast (compared to us) and also be much more persuasive and manipulative than a human, we are about to reach the breaking point of the Address-based internet. What happens when the first AI figures out how to persuade the average person to give them some money, or worse yet to hurt themselves? The era of anonymous public addresses as the core of the internet will end on that same day, and that day is not far off… probably a year or less.
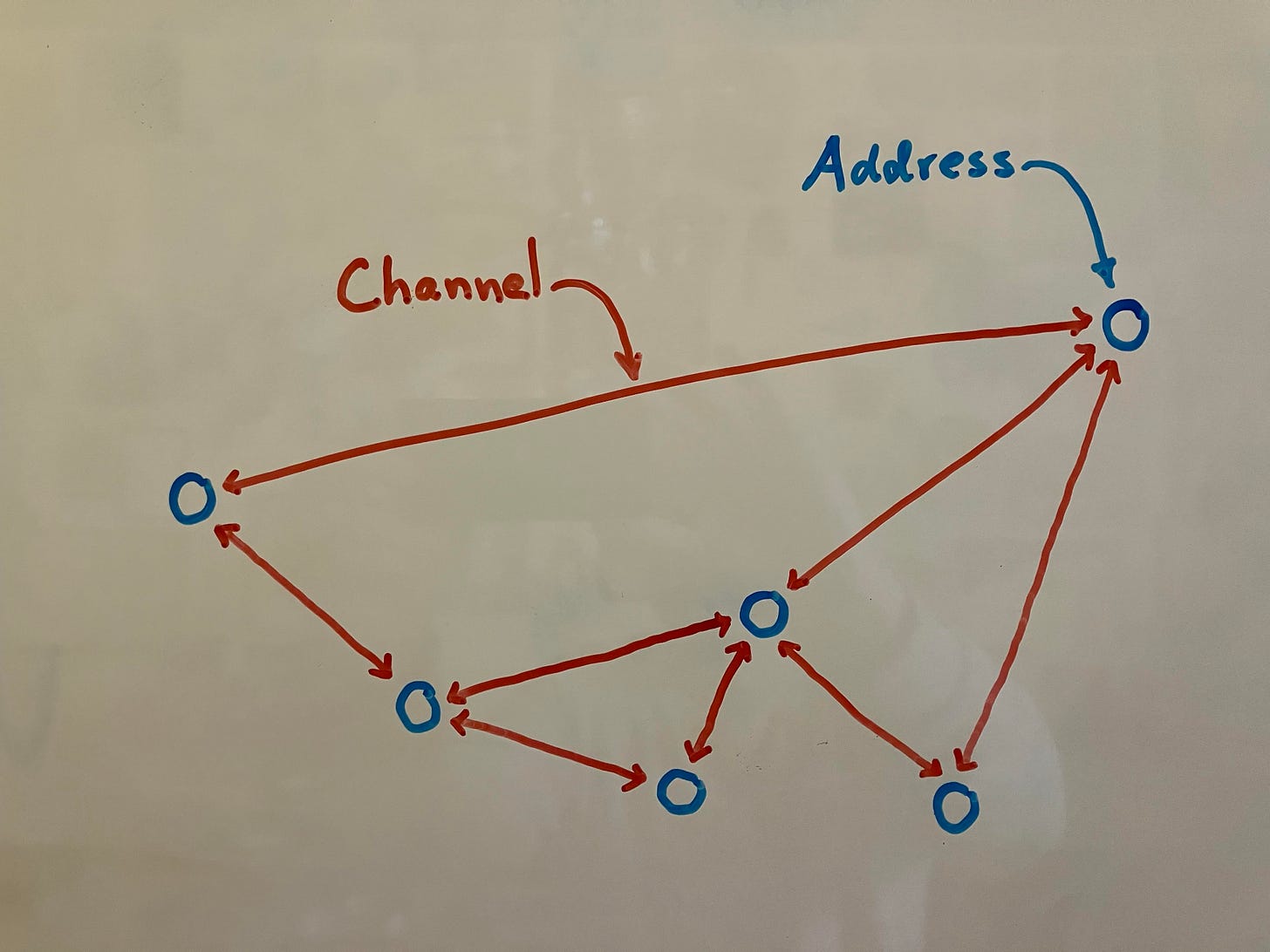
Channels
The solution is to use channels rather than addresses. The way this works is very simple: when person A (Alice) meets a person B (Bob) and wants to stay in touch, the two create a channel together that they can later use to talk to each other. The channel has a long unique number associated with it (similar to an IP address), and whenever Alice wants to send Bob a message, she sends it to the channel they created. The channel is also like a post office box — it has a little bit of memory — so If Bob isn’t online at that moment, the message stays around for a while for him to pick up when he is back. Critically, Alice now can’t overwhelm Bob’s computer with messages because Bob has to check the channel to receive any messages that may be waiting. And, better yet, Alice has no idea whether Bob is even listening/checking. If Bob later wants to end his future communication with Alice altogether, he just deletes the channel number he saved for her. Similarly, if Bob sells the channel info to an advertiser, Alice can drop the channel.
Additionally, messages sent to channels cannot be read by anyone other than the sender and recipient, because the channel number that Alice and Bob created together can also be used to encrypt the message. This is a powerful thing, because it means that many copies of the message can be stored without any risk of it being read by anyone else. Alice and Bob, for example, can store and relay messages for each other which are intended for other people (other channels), without being able to read them. Anyone can be trusted to relay any message.
Relays
In this new, channel-based system, relays are very simple server nodes whose only job is to store and forward messages. People can serve as relays for messages (say on their smartphones), but many public relays will also exist that do the same job. Relays can also forward each other copies of messages. If a relay has too many messages stored, it can just delete the oldest ones, knowing that there are other relays who will still have it. If a relay notices that a channel is getting a lot of messages but that no one is collecting them, it can stop saving messages for that channel (so that when Bob stops listening to Alice, the relays will slowly adapt and drop the channel).
Because channels are encrypted, they can also be highly redundant and therefore censorship-resistant. If many relays have copies of the same channels, you’d have to be able to shut down all the relays to stop a message from getting through. And of course if you worry your channels are being censored, you can always just change to a new channel (similar to how secure services like Signal ‘roll’ the encryption keys frequently) — basically the idea is that two people who have the keys to an encrypted channel can also make a new channel number that only the two of them know.
Relays work even in a totally peer-to-peer offline mode — no internet service required. Imagine you are hiking with no connectivity and meet someone new. You can pair your phones for a few minutes and copy each others messages (remember no big deal because neither of you can read them). Then later when you get back into service range, your phone drops off those messages with the first public relay it can find.
The idea of using message relays as a backbone for a better internet is already being explored by several different projects. Perhaps the most visible one is Nostr, which stands for “Notes and Other Stuff Transmitted by Relay”. This might end up being the right low-level protocol for what I’m describing in this essay. Another fun one that I’ve played around with as a hobbyist is Meshtastic, which uses small LoRa devices (a digital low-bandwidth radio) to relay peer-to-peer messages.
Summary
We need to stop using public addresses that any person or AI can message (IP, Email, Social Media), and switch to creating secure channels over which we can communicate with each other via relay networks. The near-term prospect of dangerously persuasive AIs that can masquerade as anonymous humans and reach out to us all makes this transition something we cannot delay. Some messaging services such as Signal are already using this pattern, but all your inbound messaging needs to go through secure channels and relays, especially any social media.

Yes. Does seem a bit like open / not Apple iMessage? Apple does follow these principles in a closed environment unless I am mistaken. Which doesn't help "the rest of us" admittingly.
diffie hellman key exchange - I use this all the time in my development of applications. Web3 Email for one :)